THE VALUE OF OUR ONLINE IDENTITIES FOR CYBER CRIMINALS
Online identities are an integral part of our daily lives. Almost all of our online activities such as social networking, shopping, banking and private communication as well as business communication, are bound to our digital identities. Even fields of our lives that are extremely critical from privacy perspective such as healthcare and governance are nowadays digital and require our identification based on our online identity. The ongoing digital transformation of our lives determines our online identity as one of our most valuable assets that become more and more interesting for cyber criminals.
5.6 BILLION EMAIL ACCOUNTS WORLDWIDE BY THE END OF 2019
There are approx. 5.6 Billion email accounts worldwide representing approx. 4.7 Billion unique online identities. The expectations are that by the end of 2020, the number of digital identities will increase to 5.9 Billion. In other words, there will be 5.9 Billion valuable online identities representing 5.1 Billion potential unique victims of cybercrimes such as identity theft, financial and other fraud. If the numbers are seen from financial perspective, cybercrimes that involve our stolen online identities are Multibillion Business for cyber criminals.
573 MILLION ONLINE IDENTITIES STOLEN IN 2018
The continuously increasing interest of cyber criminals for our valuable online identities is clearly derived from the fact that between 2014 and 2017 - 384 Million digital identities were stolen and compromised. The dimensions of this alarming trend are confirmed by the fact that in 2018 the amount of compromised online identities (573 Million) was almost twice the amount of the previous years. By analyzing only the first quarter of 2019, the situation becomes even worse.
THE VALUE OF OUR ONLINE IDENTITY IS MUCH HIGHER THAN WE THINK
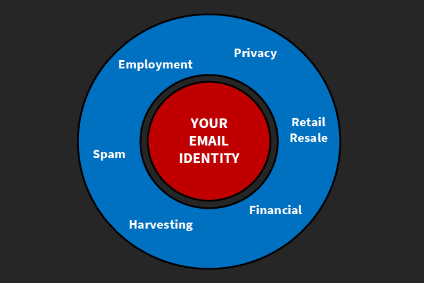
Part of the reasons for this alarming trend is the insufficient overall awareness of society about the value of our online identity. One of the common misbeliefs is “I don’t do online banking and I don't store sensitive information. Therefore, why would somebody want to hack me?” What we often forget, is that we live in the era of the digital revolution that continuously transforms every aspect of our lives within the digital space. Even if cyber criminals cannot generate direct financial value from our online identities, they will do this in an indirect way.
THE PROTECTION OF YOUR ONLINE IDENTITY IS OUR MISSION
The team of experts staying behind the BULIDSEC Email Identity Guard have more than 25 years of experience in the cyber security field. The most experienced of us have been working in various technical and management positions, fighting against cyber criminals for years. During the years, the BULIDSEC Email Identity Guard experts built an extremely broad personal network of cyber security experts from all over the world and a unique set of connections and various sources in the underground cyber space. These are utilized daily for the identification of new data leaks (identity theft) that contain exposed email account credentials and further privacy related information, such as names, addresses, phones, payment data, etc.
In addition to the 24/7 personal monitoring and investigation for stolen online identities, we built a novel set of machine learning and AI based algorithms, running continuously in the BULIDSEC Email Identity Guard cloud that perform big data analysis of million suspicious data sets that we discover daily in the underground cyber space.
Time is one of the most important factors, when it comes to stolen and compromised online identities. By being 5 days on average faster than competitors, the BULIDSEC Email Identity Guard protection services significantly minimize possible financial and trust damage that our customers may experience if their digital identities are part of a data leak. Our customers rely on 7 years of history of identified privacy-related data leaks (identity theft).
HOW DOES BULIDSEC EMAIL IDENTITY GUARD PROTECT YOUR ONLINE IDENTITY?
Living in the time of the fourth industrial revolution, where most of our lives take place in the digital world, we believe that everyone deserves an affordable, transparent and simple online identity protection.

The BULIDEC Email Identity Guard is built as a lightweight application that is extremely simple to install and to use. It does not require any specific computer, IT and cyber security knowledge or skills. You need to invest less than 5 minutes of your valuable time in turning on the BULIDEC Email Identity Guard protection shield over your online identity.
After downloading and installing the application on your machine, you need to provide a list of your digital identities that you want to protect. The BULIDEC Email Identity Guard continuously monitors your online identities by verifying them with the BULIDEC Email Identity Guard cloud. If one or more of your online identities become or were part of an identity theft, the BULIDEC Email Identity Guard will straightforward notify you by providing a complete list of identity theft cases containing your online identity from the last 7 years. In addition to the findings, the BULIDEC Email Identity Guard will provide you with easy to follow recommendations that will assist you in remediating the risk and help you to ensure the ownership over your own online identity.
BENEFITS OF PROTECTING YOUR ONLINE IDENTITY WITH THE BULIDEC EMAIL IDENTITY GUARD
-
SMART REAL-TIME IDENTITY PROTECTION
The BULIDEC Email Identity Guard is transparently monitoring your online identities in the background. Fast reactions in case of identity theft are achieved in an intelligent way even though they are not influencing at any time the performance of your device.
-
COMPREHENSIVE ALARMING IN CASE OF IDENTITY THEFT
Clear and informative real-time alarming in case your online identities are compromised, providing a comprehensive list of recommendations to help you remediate the danger in minutes and ensure the ownership of your own digital identity.
-
PROTECTION OF ALL ONLINE IDENTITIES IN LESS THAN 5 MINUTES
One simple to use tool for all your online identities that does not require any specific computer, IT or cyber security knowledge. You are less than 5 minutes away from protecting your digital identities.
-
YOUR PRIVACY DATA STAY YOUR PRIVACY DATA
The BULIDEC Email Identity Guard only requires one or more of your email addresses for protecting your online identity. The protection service does not access, process or store any other of your personal data, such as passwords, credentials, contacts, email or other communication.
-
WE DON'T BOTHER YOU WITHOUT A REASON
We believe that the best protection tool is the one that you don't notice. The BULIDEC Email Identity Guard does not use unnecessary annoying notifications. The online identity protection is there to help you focus on the important things and not to distract you.
-
FREE 24/7 EMAIL SUPPORT AS PART OF THE SERVICE
We are aware how stressfull it is, when you become a victim of identity theft. The BULIDEC Email Identity Guard protection service contains a free 24/7 support that helps you to manage such situations in the best possible way.
WHAT OUR CUSTOMERS SAY ABOUT THE BULIDSEC EMAIL IDENTITY GUARD
-
Many of my daily activities take place online. From buying travel tickets, dating with friends through various social media, weekly grocery shopping, watching TV via Netflix and Co. For my online activities, I always use different passwords in combination with all security-related mechanisms of the individual online services, such as various types of two-factor authentication. Nevertheless, my online identity has been compromised several times. By using BULIDSEC Email Identity Guard, I can now continuously and independently monitor my online identities, and apply the recommended by BULIDSEC measures, when appropriate.
Susan F.Trust is good – Control is even better
-
As many people from my generation, I use Internet to mainly communicate with my childrend and grand-children, to read news and to do some shopping. All these online services are connected to my email account that had been already compromised by cyber criminals. I am impressed that even a person with less IT knowledge like me can benefit from the BULIDSEC Email Identity Guard protection.
Karl Heinz M.GREAT PRODUCT WITH GREAT SERVICE THAT IS ALSO SIMPLE TO USE
-
Significant part of my day takes place online. This includes my job, private financies, shopping and social activities. I have 10 email accounts that are used for the various online services that I consume every day. The BULIDSEC Email Identity Guard protection met my expectations. It is simple to use and I do not worry anymore that someone can misuse my Email Identities.
Robert G.THANK YOU FOR THE FIRST CLASS EMAIL IDENTITY PROTECTION
LEARN MORE ABOUT THE MONITORING AND PROTECTION OF ONLINE IDENTITIES
CityJerks Data Breach: Safeguarding Your Online Life
In an age where our digital footprints are increasingly becoming a core part of our lives, the recent CityJerks data breach has once again reminded us of the critical importance of protecting our personal information. With millions of accounts compromised, the fallout from this breach serves as a wake-up call for both individuals and organizations […]
The Largest Data Breaches of All Time
Identity theft is at an all-time high. Not even the large, well-known online services seem to be immune to hacks, as recent data breaches at Reddit, Twitter and LinkedIn show. In this blog post, we will take an in-depth look at some of the largest data breaches of all time and find out how to […]
Best Practice for Protecting Email Identities
As ever more services are moving online, your email address is becoming the cornerstone of your digital identity. No wonder that cyber criminals have begun to target email addresses for identity theft, financial fraud and other online crimes. Make sure you know what cyber criminals are up to so you can defend yourself against digital […]






